With technology being so ever-evolving, it also presents a whole bucket of snakes to many users and particularly the most vulnerable. Many companies & innocent individuals have been affected by this bucket of snakes — both old & new snakes. Some even lose their life savings or sensitive information over some hackers’ self-acclaimed “curiosity”. Having a basic understanding of these attacks can help a great deal in recognizing & potentially saving your company, yourself & many others from these threats. Awareness is vital. Knowledge is key.
This article will dive into understanding & recognizing some cyber threats. It will not cover every example for each attack or every attack. Neither will it be an in-depth coverage as it will only cover a few commons one you or your company need to look out for.
1. Malware
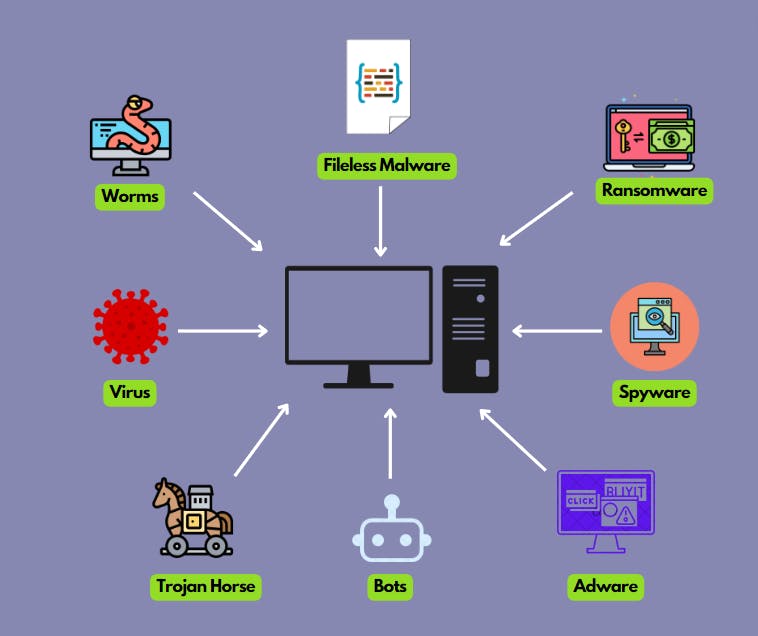
An illustration of a few types of malware.
Simply put malware is some malicious hardware, software, or firmware that is being inserted into a system to gain unauthorized access to it & to cause damage.
There are several types of common malware:
Virus
An application that attaches itself (like a leech) to programs in order to alter the data or even delete it. And usually without the user’s permission.
This can be downloaded by clicking a link sent to you by a foreign email or one you’ve found & clicked on from someplace else on the web.
Adware
Software that shows advertisements on your web browser & causes performance issues.
You’ve noticed that a website you’ve visited has been projecting lots of ads & it’s also starting to slow down the page, then most likely the computer or device has been affected by adware.
Spyware
It is code that is downloaded without user authorization that, as the name suggests, spies on any information or data the user has or types in on their computer. This sensitive data can then be relayed to a third party & used by them to harm the data owner.
If you type something on your computer & it takes a while for it to display on your screen, it’s probably due to spyware. Now, this works in conjunction with a keylogger being embedded into it that essentially records whatever you type in including your passwords.
Ransomware
Maybe you aren’t allowed access to your data. Or perhaps the hackers are threatening to publish your sensitive information online under one condition — that you pay them whatever amount they tell you to pay.
This is a case of ransomware.
Worms
Unlike a virus, a worm is some code that makes copies of itself from one device to another without human interference which is exactly how it spreads.
Perhaps someone at work sent the same email to everyone in their contact list that also has the same subject line as the foreign, malicious email that they’ve received — this is an example of a worm.
Trojan Horses
Similar to spyware, it disguises itself as legit software so that the user downloads it and allows hackers access to the user’s system.
A common way hackers disguise themselves & their intentions is by masquerading as legitimate anti-virus software.
2. Phishing
An illustration of phishing.
This has total reliance on social engineering. That is to say, the hacker relies on what is seemingly a normal human interaction with the user to extract critical information. The attack usually starts off directly on the user.
There are several types of phishing attacks:
Vishing
Smishing
Spear Fishing
Whaling
This attack could be through an email with a malicious link included in it, calling the user as a banker from the user’s bank to ask for this information, or sending a text message instead with the malicious link in it.
3. SQL Injection

An illustration of SQL Injections.
SQL injections are the type of attacks that use the SQL database language to extract information & manipulate data from an application’s database. Ultimately, it also damages the database. This will actually be a query that is injected when a user inputs their data in the application that has to be processed & saved in the database.
There are several types of SQL Injection attacks:
Union-Based Injections
Boolean-Based Injections
Error-Based Injections
Out-of-Band Injections
Time-Based Injections
One tell-tale sign of SQL Injections is the application continuously behaving differently than what is expected or content being changed than expected.
4. Cross-Site Scripting (XSS)
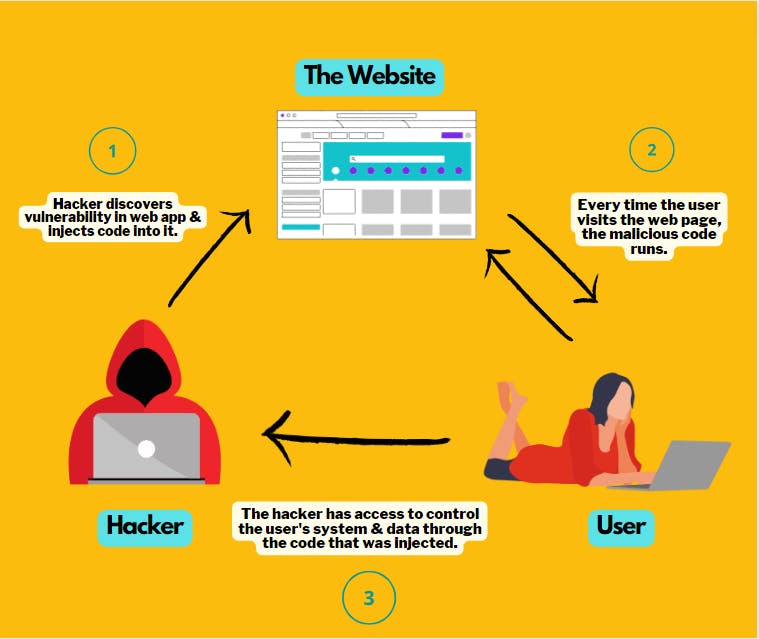
An illustration of a Cross-Site Scripting (XSS) attack.
This deals with a security vulnerability in the web application & sites, especially the ones in which the user interactions involve user inputs (e.g forums & commenting). The attacker can enter malicious code into the web application using a browser-side script. When a user visits the web app & puts in their input (e.g login credentials), the malicious code executes giving the hacker control of the user’s browser & system or stealing sensitive information.
Here are the types of XSS attacks:
DOM-based XSS
Reflected XSS
Stored XSS
One example is if you notice that you can’t seem to control your browser when visiting a website, then this is an XSS attack being deployed. And of course, this is just one of many signs.
5. Cross-Site Request Forgery (CSRF)
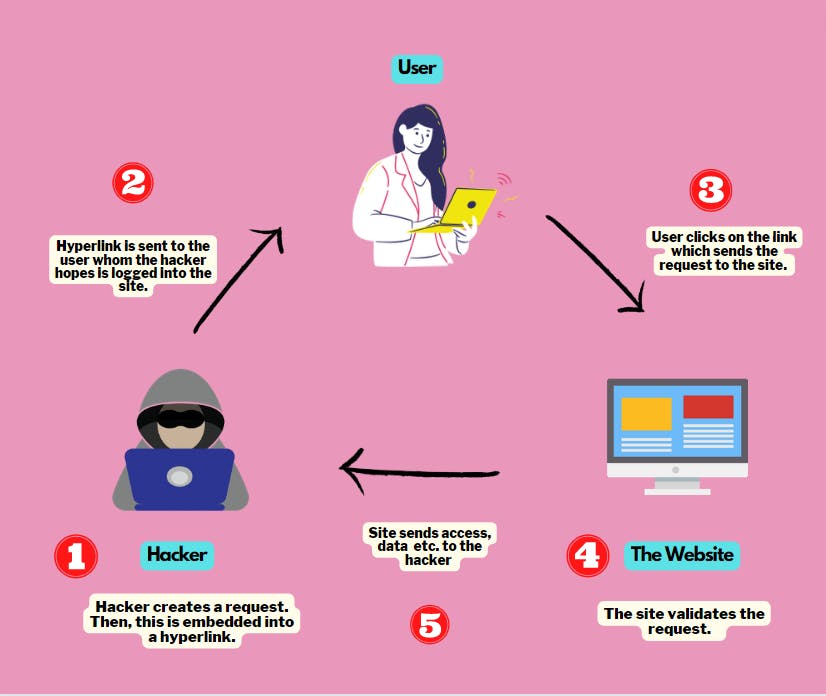
An illustration of a Cross-Site Request Forgery (CSRF) attack.
This is another web security vulnerability where a user of a site visits it through a link sent by the attacker who hopes that the user is logged into their account on the site.
During this session, a user under their authenticated account can do all sorts of things such as change their password, interact with other features of their account & transfer funds. In which the site will validate their request and sends all of that data, access, funds, etc back to the attacker.
This link can be sent to a user through malicious emails, blogs, or websites to name a few.
6. DDoS Attacks
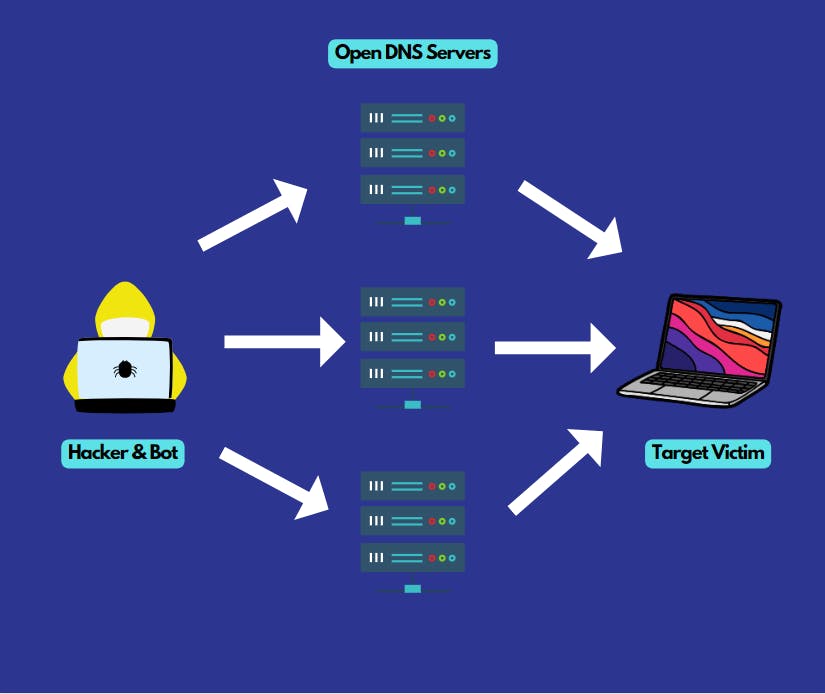
An illustration of a DDoS (Distributed Denial of Service) attack.
DDoS (Distributed Denial of Service) attacks target a network in order to ‘deny’ services to its users. It basically denies users of the network access to resources provided by it.
The attacker uses multiple remote locations (usually with the help of botnets) in order to execute the attack on the network. They would flood the network with so much internet traffic that the network will in a sense, collapse & shut down. A network can only take in so much traffic at a time.
The common sign of a DDoS attack is when a site becomes unavailable or resources are unavailable. Especially, when it is down for a period of time.
These are just some bare-bone examples of these cyber crimes along with what these attacks comprise. There are also attacks where most of these threats are combined or layered together. So it is a good headstart to be informed of what they are and the many clever ways that cybercriminals use to trap their victims.
I hope that you’ve found this article informative enough. Not only for yourself but many others who may be easy targets for these attacks.
If you have any comments or suggestions, please feel free to do so. You can find me on GitHub & LinkedIn.
Also published on HackerNoon, Medium & DEV.to Community.